EMERGENCY
News
• Nov 12, 2020
Analysing the fall 2020 Emotet Campaign
Neurosoft through its cybersecurity solution #Neutrify, in cooperation with the University of Piraeus and Athena Research Center are releasing today a white paper analyzing Emotet’s latest attack which has had a significant impact in several countries worldwide.
The paper leverages the data of a specifically crafted dataset, which contains emails, documents, executables and domains from the latest campaign. It aims to analyze the attack vector, map the infrastructure used in various stages of the campaign and perform a surface analysis of Emotet’s malicious payloads, in order to assess their potential impact. The utilized dataset consists of 3048 e-mail headers, 1968 documents, 749 executables and 1375 domains which have all been extracted from these malicious documents.
The samples have been collected from public feeds, and clients monitored by Neurosoft, while the e-mail headers are from Neurosoft clients and a big Greek financial institution. For the anonymity of the clients, all recipient related information has been removed prior to the analysis of the e-mail headers. The bulk of the above information belongs to the past few months, during which Emotet has re-emerged after several months of inactivity, with the analyzed e-mails covering the recent spike in Emotet traffic on which Neurosoft has issued relevant alerts (see https://www.linkedin.com/posts/neurosoft_emotet-30102020pdf-activity-6727979532613169152-YtQV, https://twitter.com/neutrify/status/1317076024035856384, https://neurosoft.gr/wp-content/uploads/2020/10/Emotet-16.10.2020.pdf).
You can find the whole paper here and the report's publishable Indicators of Compromise (IOC) here.
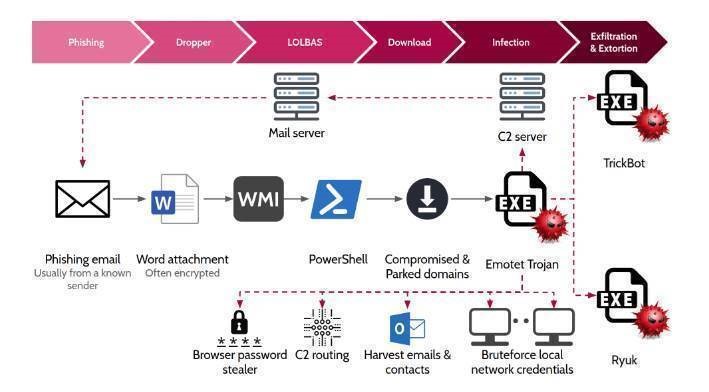
Figure 1: Emotet’s latest Campaign modus operandi
Read Next
Apr 23, 2026
Cybersecurity in Greece: 4 Ransomware Risk Drivers
Apr 16, 2026
SOC & NOC View: What We’re Seeing in Cybersecurity
Start your journey
Our team of seasoned experts is dedicated to delivering tailored solutions that perfectly align with your specific business needs and objectives. Do you want to help you navigate your path to success?