EMERGENCY
Your refreshing tech break


Cyber
• Apr 23 2026
Cybersecurity in Greece: 4 Ransomware Risk Drivers
Cyber
• Apr 16 2026
SOC & NOC View: What We’re Seeing in Cybersecurity
Technology
• Apr 6 2026
Zero Trust in Practice: Why the Perimeter Was Never Enough
Cyber
• Mar 30 2026
Observability or Monitoring? Building Resilient IT Ops
Events
• Mar 23 2026
Neurosoft & Microsoft Unite Against Ransomware Threats
Cyber
• Mar 17 2026
Inspiring Next Gen: From School to Cybersecurity Communities
Events
• Mar 12 2026
Award-Winning Endpoint Security Strategy for Modern Business
Cyber
• Feb 25 2026
Neurosoft Quiz - Are you ready to play?
Cyber,
News
• Jan 26 2026
TAISE Credential & AI-Powered Cybersecurity Services
Field
• Jan 21 2026
Field Services in FTTH: 2026 Trends with a Focus on Quality
Cyber,
Technology
• Jan 15 2026
Project Management: How the Theory Becomes Reality
News
• Nov 27 2025
Neurosoft in Action: The November Edition
Cyber
• Nov 14 2025
Cut Security Costs, Not Business Safety with CISOaaS
Cyber,
News
• Nov 7 2025
Microsoft Specialization in Cybersecurity Achieved
Cyber,
News
• Nov 3 2025
OT Security: The Importance of a Focused Strategy
Cyber
• Oct 30 2025
The Thorn in My Website: Cybersecurity Awareness Month
News
• Oct 24 2025
Pink@Work: Awareness Doesn’t Stop at Cybersecurity
Cyber
• Oct 20 2025
Compliance Automation: Business and Technology Leaders Ask
Events
• Oct 9 2025
Cisco Connect: The Next Day of Secure Networking
News
• Sep 30 2025
Great Place To Work: Our People, Our Investment
Cyber,
Events
• Sep 18 2025
Fortinet Security Day: A Day Devoted to Cybersecurity
Field
• Sep 10 2025
FTTH or Broadband? Make an Informed Choice
Cyber
• Sep 4 2025
Compliance with NIS 2: A Starting Point to Cyber Resilience
Cyber
• Aug 7 2025
Awareness: Your Summer Security SPF
Cyber
• Jul 30 2025
Beach Season or Breach Season?
Field
• Jul 25 2025
FTTH: A Digital Transformation Enabler
Cyber,
Technology
• Jul 22 2025
POV: Remote Work Setups & Summer Cybersecurity
Cyber
• Jul 18 2025
The Key Factor in Choosing a Cybersecurity Solution?
Cyber
• Jul 15 2025
4 Expert Tips to Reduce Data Breaches
Cyber,
Events
• Jun 27 2025
Elevating OT Security
Cyber,
Events
• Jun 23 2025
Two Days of Cybersecurity & Ethical Hacking
Cyber,
Events,
Technology
• Jun 17 2025
Microsoft AI Tour: A Strategic Bulletin for AI Innovation & Cybersecurity
Field
• Jun 5 2025
Corrective Maintenance Field Services: Minimizing Downtime
Technology
• May 28 2025
Microsoft Advanced Specialization in Cybersecurity Achieved
Technology
• May 21 2025
Information & Communication Technology Sector: Last Updates
Events
• May 15 2025
Westcon Awards 2025: Best Cloud Partner
Cyber
• May 5 2025
Corporate Cybersecurity: Top 3 Behavioral Observations
Field
• Apr 30 2025
Preventive Field Services for Lower Costs and Customer Satisfaction
News
• Apr 22 2025
SD-WAN, a Single-Player?
Cyber
• Apr 14 2025
NIS 2: Compliance at a Glance
Events
• Apr 7 2025
Cybersecurity and Investments in AIM Congress
Field
• Mar 27 2025
The Power of Rollout Services: Ensuring Seamless Technology Deployment
Cyber
• Mar 27 2025
The SOC Landscape: One Size No Longer Fits It All
Cyber,
Events,
News
• Mar 27 2025
Cybersecurity Awards 2025: A Triple Celebration for Neurosoft
Technology
• Mar 26 2025
Moving Beyond Fragmented Cloud Security with Unified SASE
Cyber
• Feb 26 2025
NIS 2 Compliance? Your Most Common Questions Answered
Cyber,
Events,
News
• Feb 20 2025
Unlocking the NIS 2 Directive: Embracing Compliance as Your Ultimate Strategy
Cyber,
Technology
• Jan 24 2025
Neurosoft OT Security Service v2.0: Redefining Protection for Critical Infrastructure
Events,
News
• Jan 20 2025
30 Years of Excellence & Growth: Happy Birthday to Neurosoft!
Cyber,
Technology
• Nov 28 2024
The Importance of OT Security in Protecting Critical Infrastructure
Cyber,
Events
• Nov 22 2024
Highlights from Neurosoft at the Inaugural Cyber Security Forum
Cyber
• Nov 13 2024
Neutrify: Moving Beyond Traditional SOC Services
Technology
• Nov 7 2024
SASE, a Game-Changer for Modern Businesses
Technology
• Oct 31 2024
Enterprise Link 2.0: Business Secure Connectivity Redefined
Cyber,
News
• Oct 22 2024
An Amazing Milestone for IR & TI Neutrify’s Team
Cyber
• Oct 7 2024
Navigating NIS 2: What Businesses in Greece Must Know
Events,
Technology
• Sep 27 2024
Neurosoft, Gold Sponsor of the Cisco Experience 2024. Together, we are shaping the digital future!
Field,
News
• Sep 26 2024
Our Supply Chain Department & Repair Lab Is On The Move!
News
• Sep 17 2024
Celebrating the Unsung Tech Heroes: A Tribute to Our IT Professionals
Cyber,
News
• Aug 9 2024
Stay summery, connected and secure!
Cyber
• Jul 23 2024
Top summer Cyber Threats: Who is the winner?
Cyber,
News
• Jul 22 2024
2024 CrowdStrike Incident: Do You Effectively Manage your Third-Party Vendors?
News
• Jul 17 2024
9,000 and Summery! Our LinkedIn Community is getting bigger and bigger
Cyber
• Jul 8 2024
Cybersecurity Posture Evaluation for SMEs
Technology
• Jun 28 2024
Retail Revolution: Securing Your Business with SD-WAN Solutions
Technology
• Jun 17 2024
Don’t go traditional. Go Microsoft Defender for Business with Neurosoft!
Cyber
• Jun 3 2024
Ensuring Business Continuity: How DORA & NIS 2 Shape Your Strategy
Cyber
• May 27 2024
NIS 2: The road to Compliance is not a “How to” game
Cyber
• May 16 2024
Neurosoft’s Holistic Readiness Approach: Compliance through Simplicity
Events,
Field,
News
• Apr 29 2024
Nokia Wavelengths EMEA-LAT: A successful cooperation with Neurosoft
News
• Apr 25 2024
Greece Embraces the Future: FTTH Poised for Growth
News
• Apr 24 2024
DORA: Α crucial regulation for organizations in the EU financial sector
Cyber
• Apr 11 2024
Ransomware Victimization: Do personality types matter?
Events,
News,
Technology
• Apr 4 2024
Neurosoft: Huawei Valuable Contribution Partner for 2023!
News,
Technology
• Mar 27 2024
FortiSASE and Enterprise Link 2.0: A powerful alliance
News
• Mar 20 2024
8,000 Strong and Growing! Celebrating Our LinkedIn Community
Cyber,
News
• Mar 11 2024
vCISO and the future of Cybersecurity
Cyber,
Events,
News
• Mar 8 2024
Cybersecurity Day #2: Imperative implementation of NIS 2
Cyber,
Events,
News
• Feb 29 2024
Neurosoft Cybersecurity Day #2: One week left
Cyber,
News
• Feb 29 2024
NIS 2 and Security Maturity Assessment: A speed race towards Cybersecurity maturity
Cyber,
News,
Technology
• Feb 12 2024
Neurosoft OT Security Service: Are You Ready for the Future of OT Security?
Cyber,
Events,
News
• Feb 10 2024
Neutrify: Ηarnessing the potential
Events
• Jan 29 2024
Neurosoft Cybersecurity Day #2: Save the date
Technology
• Jan 10 2024
Enterprise Link 2.0: A new era of secure connectivity for businesses
Technology
• Jan 3 2024
Preveza Marina: Moored, connected and secure
Cyber,
Events
• Dec 19 2023
Feel the Xmas spirit but do not nibble the bait: Α complete Ransomware guide
Events,
News
• Dec 15 2023
Neurosoft is celebrating with you and dressing up for Christmas!
News,
Technology
• Dec 12 2023
Stay Xmas-ed, Cloud-ed and secure
Cyber,
News
• Nov 28 2023
Achieving Excellence in Cybersecurity: Neurosoft's Holistic Approach
News
• Nov 14 2023
“Managed Resignation”: The role of the MSP in a time of Crisis
Cyber,
News
• Nov 9 2023
Is Cybersecurity a science?
Field,
News
• Nov 9 2023
Telecom Infrastructure: Neurosoft is leading the way
Field,
News
• Nov 2 2023
Cablenet project: A successful tripartite partnership
Cyber,
News
• Oct 26 2023
Cybersecurity Awareness: A never-ending process towards business resilience
Cyber,
News
• Oct 16 2023
Ransomware Readiness Assessment: The most essential security assessment for the modern business
Cyber,
News
• Oct 12 2023
MDR-Backed Incident Response: Boost Your Security with Neurosoft’s service
Events,
News,
Technology
• Oct 4 2023
Enterprise Link 2.0 : A high digital security solution for businesses
Cyber,
Events,
News
• Sep 22 2023
ΔΕΗ BITE Awards 2023: Two Gold Awards for Neurosoft
News
• Sep 11 2023
7,000 LinkedIn followers and counting!
Cyber,
News
• Sep 11 2023
vCISO: Specialized consulting services for any organization or business
Events,
News
• Sep 6 2023
Neurosoft sponsors Fortinet Security Day 2023
Cyber,
News
• Aug 29 2023
Hackcraft’s Red Teaming: Developing realistic attack scenarios
News
• Jul 30 2023
Microsoft renames Azure Active Directory to Entra ID
Cyber,
News
• Jul 23 2023
QRadar XDR: How it revolutionizes the Neutrify service
Field,
News
• Jul 15 2023
Field Services: How Neurosoft ensures maximum performance?
Events,
News
• Jul 10 2023
Supply Chain Awards 2023! Two Awards for OPAP
Cyber,
News
• Jul 5 2023
SOC Visibility Triad: Why is determinant for effective Cyber Defense?
News
• Jun 30 2023
Neurosoft is a sponsor of the (ISC)² Hellenic Chapter!
News,
Technology
• Jun 28 2023
SD-WAN: The great ally of ZeroTrust
News,
Technology
• Jun 20 2023
FortiSASE: Extend your protection anywhere!
Events,
News
• Jun 9 2023
Webinar: A Walkthrough to Security Awareness
Events,
News
• May 19 2023
Webinar Registration: A Walkthrough to Security Awareness
Events,
News
• Mar 8 2023
Neurosoft's first Cybersecurity Day
Events,
News
• Oct 21 2022
“Built for full visibility and Zero Trust” Event
Events
• Jun 20 2022
1st International Cybersecurity Challenge
Events
• Mar 2 2022
Webinar - The right way to do SD-WAN
News
• Nov 9 2021
QUALCO and Neurosoft complete transaction for two subsidiaries
News
• Nov 12 2020
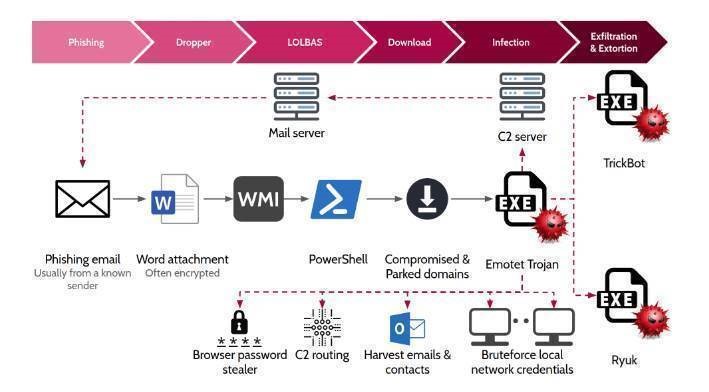
Analysing the fall 2020 Emotet Campaign
News
• Aug 6 2020
Partnership with Microsoft Corporation
News
• May 4 2020
Enterprise Link Press Release
News
• Mar 19 2020
Stay Home - Stay Connected
Events
• Jan 24 2020
Vasilopita (New Years Cake) cutting!
News
• Sep 6 2019
Neurosoft supports GRNOG
News
• Jun 26 2019
Week 6 of our NeuroSocial Q&A session
News
• Jun 19 2019
Week 5 of our NeuroSocial Q&A session
News
• Jun 12 2019
Week 4 of our NeuroSocial Q&A session
News
• Jun 5 2019
Week 3 of our NeuroSocial Q&A session
News
• May 29 2019
Week 2 of our NeuroSocial Q&A session
News
• May 23 2019
Week 1 of our NeuroSocial Q&A session has begun!
News
• Feb 13 2019
NeuroSOC Malware Analysts Detect Spam Campaign
News
• Dec 19 2018
CSR – Latest actions
Events,
News
• Nov 27 2018
Decentralized 2018 Conference
Events,
News
• Nov 26 2018
SealedGRID Platform
Events,
News
• Nov 6 2018
Neurosoft at WAN Summit
Events,
News
• Oct 26 2018
4th ShipIT Conference
Events,
News
• Oct 25 2018
Oracle Impact Event
Events,
News
• Jun 18 2018
RedyOps @Phdays
Events,
News
• May 4 2018
DFRWS 2018 Europe
News
• Feb 14 2018
Proxima+: Sales Finance of Things!
News
• Dec 5 2017
Neurosoft supports the Hellenic Cyber Security Team.
Events,
News
• Oct 26 2017
May the Angel be with you!
News
• Oct 17 2017
Vulnerability Announcement
Events
• Sep 30 2017
Cybertech Europe 2017
Events
• Jun 28 2017
Thank you for visiting us at BSides Athens 2017!
Events
• Apr 21 2017
Neurosoft at RFIx Convention- London
News
• Mar 2 2017
Itching to start playing accumulators on BetBuzz.com?
News
• Feb 1 2017
Neurosoft welcomes the ISO/IEC 27001 standard!
News
• Jan 31 2017
SNFCC: As a proof of trust, the co-operation expands!
Events
• Sep 30 2016
Training on Oracle WebLogic Server 12c: Administration I
Events
• Sep 29 2016
Neurosoft attends EBRD & FCI-IFG events in Frankfurt
News
• Sep 19 2016
New Website Launch!
Events
• Sep 6 2016
A Hacker Wisdom Experience!
News
• Nov 19 2015
Industrial Control Systems-A new target?
News
• Nov 11 2015
New International Contract in Receivables Finance
Start your journey
Our team of seasoned experts is dedicated to delivering tailored solutions that perfectly align with your specific business needs and objectives. Do you want to help you navigate your path to success?